In the last two parts of the WPA3 Authentication, we have learnt about WPA3 Dragon fly handshake and , the frame exchanges involved in WPA3.
In this post we will do a replay attack and other attack scenarios and check how the AP behaves.
Go through the earlier posts on WPA3 to understand these attack scenarios better.
Test Scenario : Doing a Replay Attack on WPA3 AP
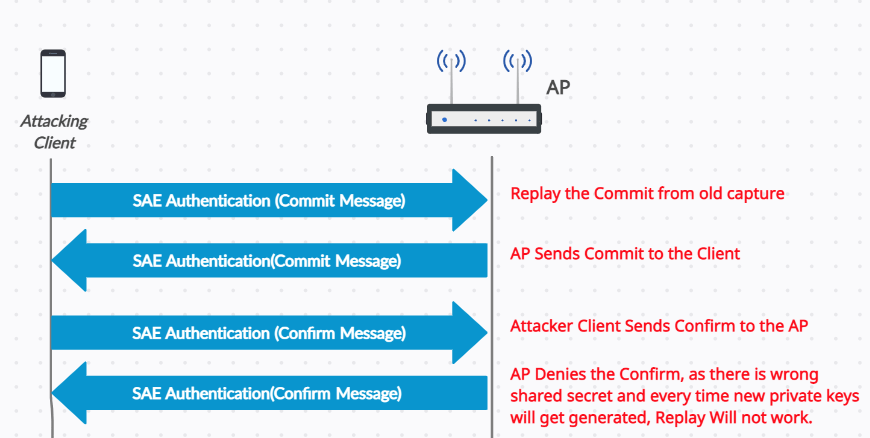
1) In this scenario, we will do the replay attack on the WPA3 AP, with the already captured authentication commit frame and we will see how the AP behaves.
2) Here we will do the replay attack for the successful handshake that was done before. You can find that successful exchange from the link WPA3-AUTHENTICATION-PART 2, We will do the replay attack for that.
Steps:
- Capture the successful WPA3 handshake.
- Send the old Authentication Commit frame (Replay).
- Now AP sends the commit back to the Client.
- Now Attacking Client sends the confirm to the Client.
- AP denies and sends the Failure to the Client , because every time new private keys get generated and the shared secret and it is different in both the AP and client.
- It fails in the Confirm phase, because the AP has verified the hash that is sent in the confirm phase and denies the request because the Hash verification is failed. AP expects the proper hash in the confirm sent by client , based on the commit exchange.
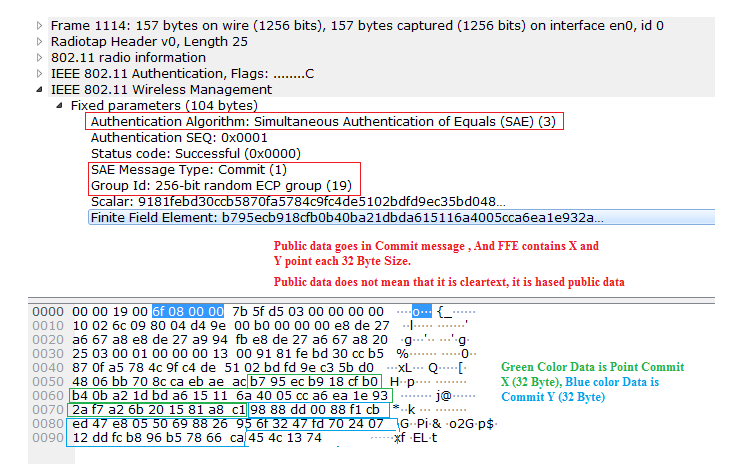
Here the below picture shows the authentication commit frame from the successful 4-way handshake.
Step 1 : Capture the commit from previous capture, from the successful 4-way handshake. [Frame No : 1114].
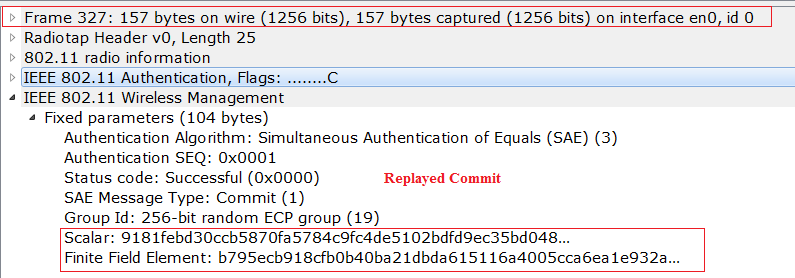
Step 2 : Now the Attacking client will send the same authentication commit to the AP, observe the below replayed commit message [Frame No : 327].
Step 3 : AP will send the commit back to the client.
Step 4 : Attacking Client will send the confirm,.
Step 5: Now AP will verify the HASH that is sent in the commit and denies the authentication, because the shared that is being generated in commit exchange is wrong.
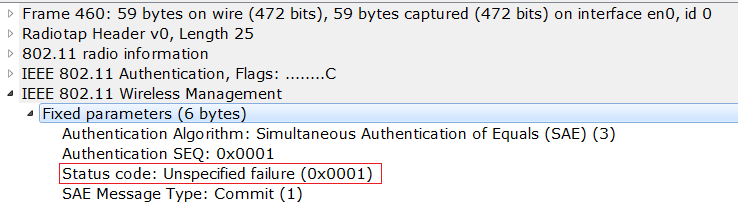
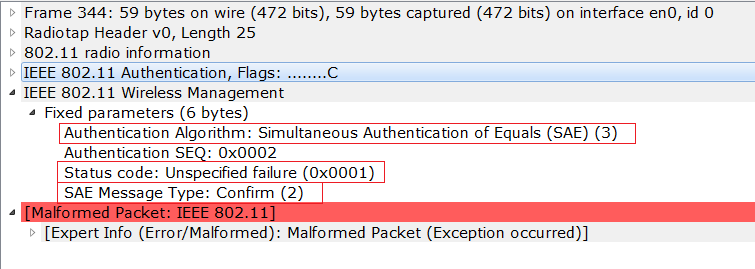
You can see the below capture that is sent in the AP confirm saying the connection is rejected.
Test Scenarios : Injecting Junk COMMIT/SCALAR values
In this section we will test the few below scenarios. All the packets are injected from the attacking client.
1) Sending the scalar value as all zeros
2) Sending the Commit X as Zero
3) Sending the Commit Y as Zero
4) Sending the Commit X and commit Y as zero
5) Sending the SCALAR Commit X and commit Y as zero
In the below all the tests authentication failures happen at the Commit that is being sent from AP to client. Observe the below diagram to know where exactly it fails for the above scenarios.

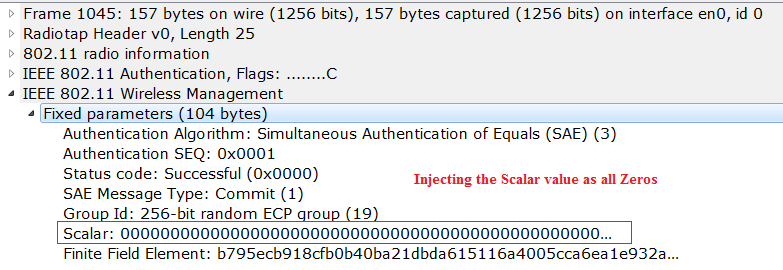
Test Scenario 1
Observe the below sniffer capture and check that we are injecting the scalar value as all zeros.
Test Scenario 2
Observe the below sniffer capture and check that we are injecting the Commit X value as Zero in the commit message.

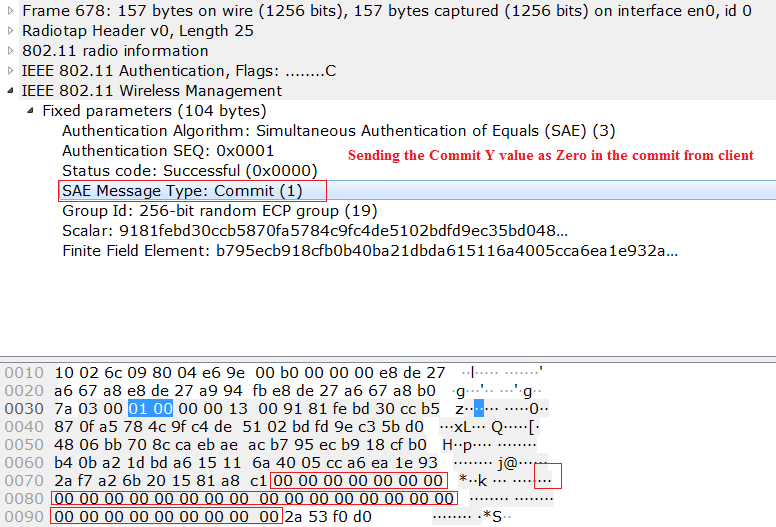
Test Scenario 3
Observe the below sniffer capture and check that we are injecting the Commit Y value as Zero in the commit message.
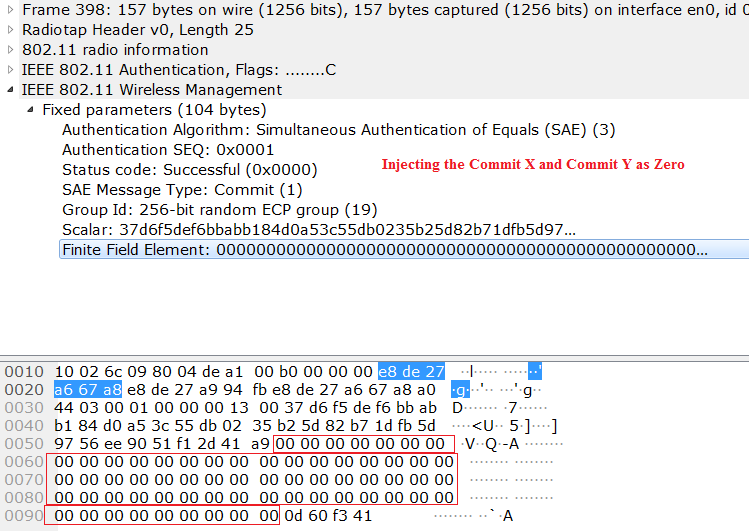
Test Scenario 4
Observe the below sniffer capture and check that we are injecting the Commit X and Commit Y value as Zero in the commit message.
Test Scenario 5
Observe the below sniffer capture and check that we are injecting the SCALAR, Commit X and Commit Y value as Zero in the commit message.
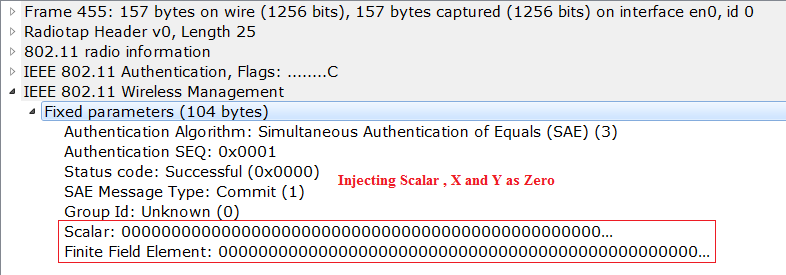
In all the above scenarios , We are trying to inject the JUNK X and Y value and scalar values. So, the AP replies with the commit failure. Observe the below commit reply from the AP for all the scenarios.