Testing and Sniffer Captures
Before you read about this post , have a look at the earlier post about the WPA3 Handshake.
In this post , we will see about the frame exchanges in WPA3 and the few test scenarios.
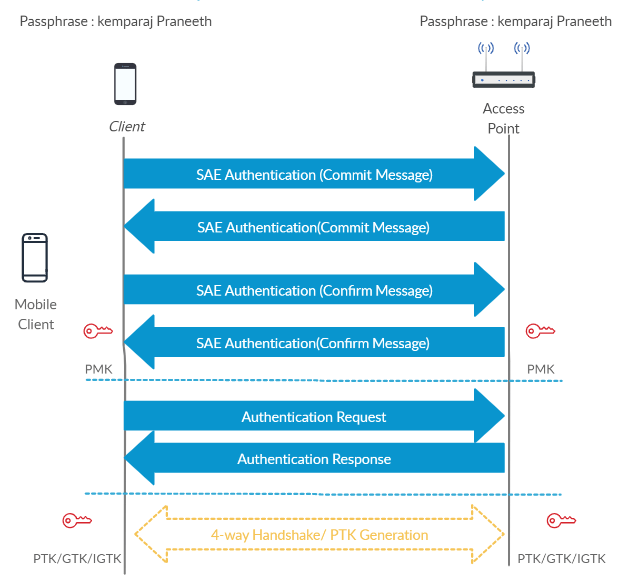
Before we go into the sniffer captures observe the below frame exchange that happen in the WPA3 Handshake.
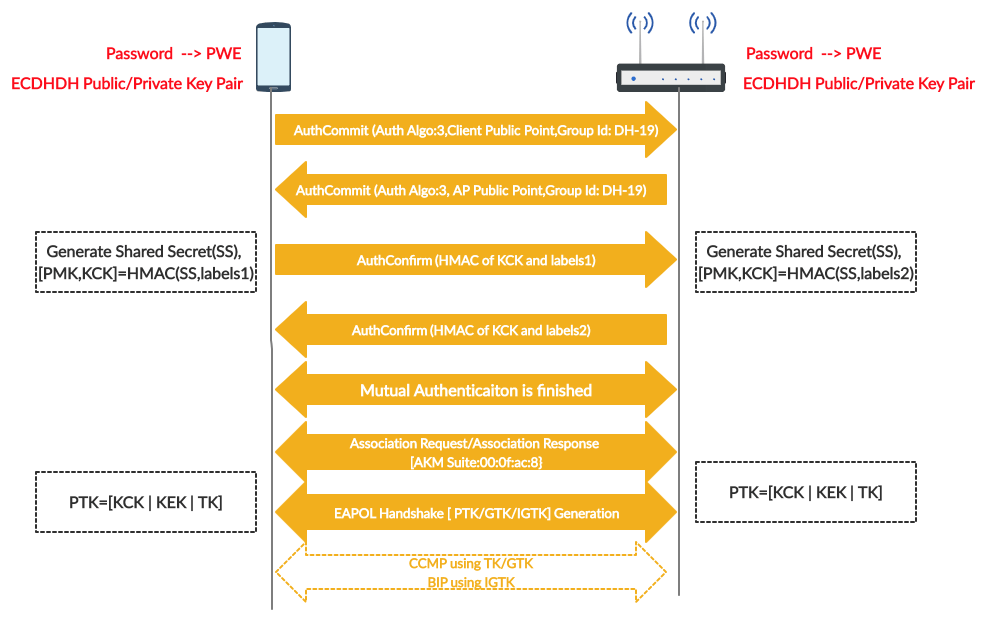
Please note that KCK in the AuthConfirm is different from the KCK in PTK
In WPA3 Authentication PMF is Mandatory. Observe the below Beacon capture from the WPA3 Network.
Similar settings will be seen in the Probe Response Frame as well.

Test Scenario : Successful WPA3 Authentication
Observe the below sniffer capture for the successful handshake procedure. I have filtered only the required frames.

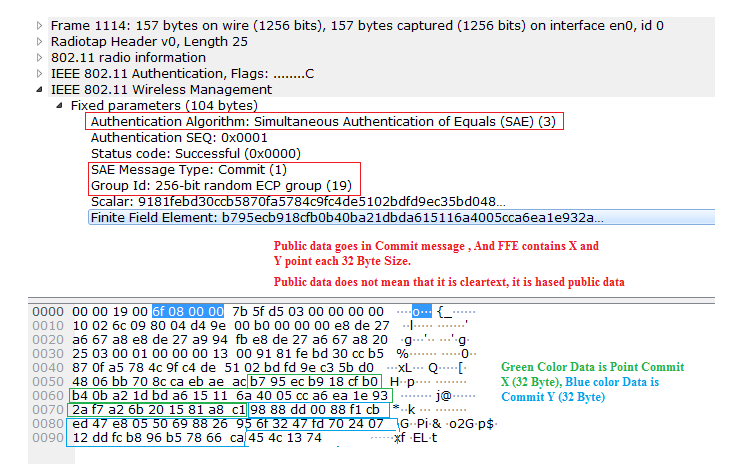
1) Now lets see the Commit message from Client to AP. i.e frame number 1114.
2) Now Lets see the commit Message from AP to client. It will also contain the scalar and FFE (i.e X and Y) i.e frame number 1116.
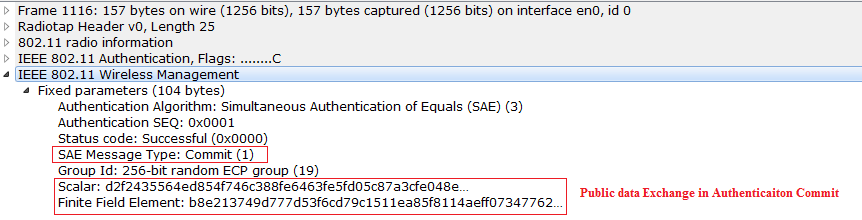
Note that public data is also encrypted. It is not a clear text.
3) At this point Both the Peers will generate the same shared secret and the hashed confirm message goes from Client to AP, and AP verifies the Confirm that is sent by Client. Observe below capture for this.
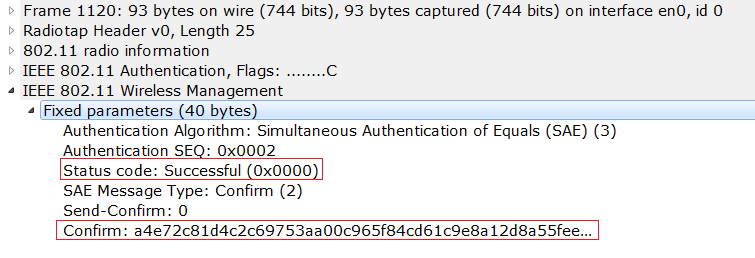
4) Confirm Message from AP to client and client verifies. So the Mutual Authentication happens here. Observe the below capture here.
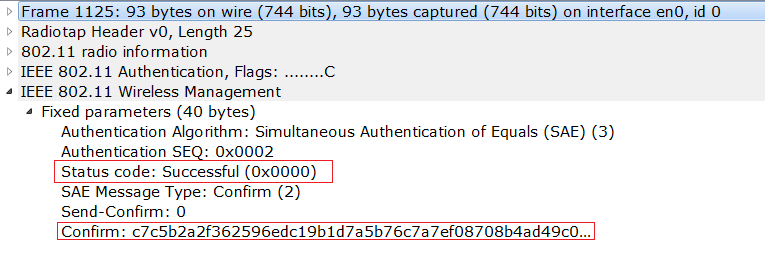
Confirm Message
You can see that Hashed Confirm message from the Client to AP , and AP to client are different, Still the Peers will be able to verify based on the inputs that they send to function.
Once the DragonFly authentication is success , PMK will be derived.
PMK in WPA3
Here PMK that got generated is not just based on the SSID and passphrase. It is based on the key generated in Diffie Helmen algorithm and Elliptic Curve Cryptography. So, here each client will have different PMK. But in the WPA2 each connected client has the same PMK.
5) See the Association Request frame below for the WPA3 Handshake.
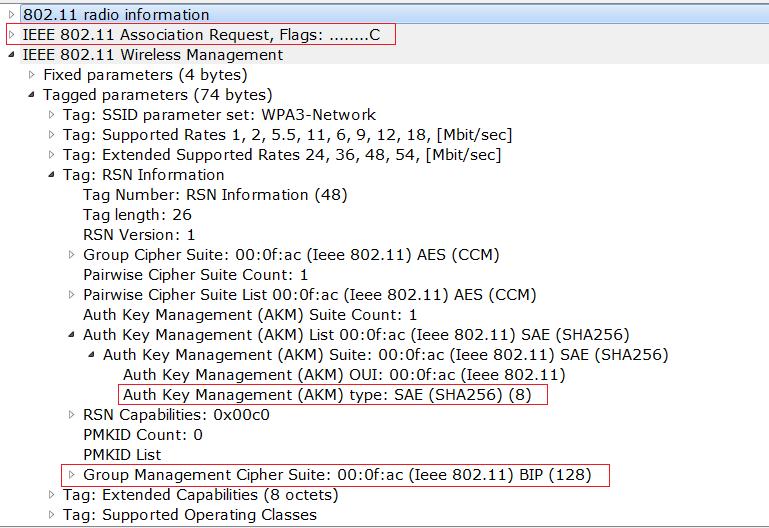
After the Association, 4-way handshake will be done based on the PMK that is generated and the required keys will be generated.
Test Scenario : Entering Wrong Passphrase
Now lets test entering the wrong pass phrase and observe where exactly it fails.
1) Client enters the wrong PIN.
2) Authentication Request (Commit) frame will be sent from client to AP
3) Authentication Response (Commit) frame will be sent from AP to client
4) In the commit exchange the Public data X ,Y will be exchanged and both the client and AP will guess the password and generate the same shared secret, if the password entered on the both AP/Client are correct.
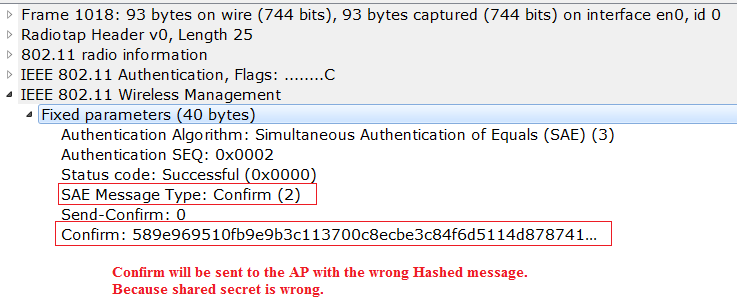
5) After the commit phase, Now client will generate the shared secret and it will send the confirm message to the AP. [Here client will generate the wrong Confirm Message] because the password entered is wrong.
6) Now AP will receive the Confirm message and it will verify the confirm message that is sent by the Client. Here the verification of the confirm will be wrong, because the shared secret is wrong. So, the AP will send the failure in the Confirm message.
Observe the below diagram to understand the flow.

Observe the below sniffer captures to understand this flow. I am not showing the commit exchange here.
See the below SAE confirm frame that is being sent from Client to AP.
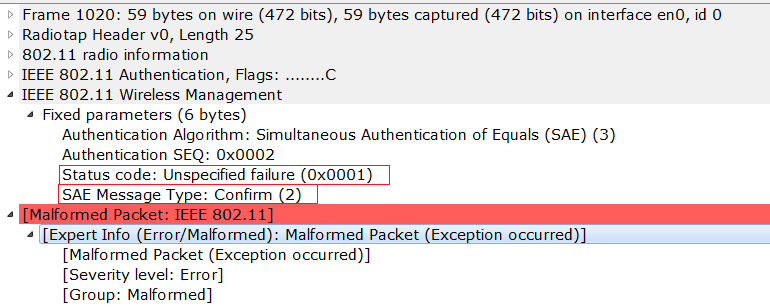
See the below confirm message that is being sent from the AP to client. But the wireshark shows it as malformed packet , as it is not able to dissect it properly. Still we can see the failure in the SAE confirm message.
That’s all about in this post. In the next post we will see the replay attack in WPA3 and few more testing scenarios and we will see how the AP behaves.