In the earlier posts we have learnt about the keys generation on 4-way handshake for WPA2,WPA2-PMF, and WPA3.
If you don’t properly understand about the Keys and keys hierarchy, you will get confused in understanding this post. Go through the below links to understand the key generation properly and proceed for better understanding this post.
4-Way Handshake keys generation for WPA2
4-Way Handshake keys generation for WPA3
In this post we will learn about the GTK/IGTK generation, how this key gets wrapped in M3, and then we will verify this in the wireshark capture.
GTK/IGTK will be sent in the M3 Message. After 802.11w, new key IGTK has been introduced and GTK/IGTK both will be sent in the M3 Message.
Standard Use AES-KEY Wrap Algorithm to wrap the GTK/IGTK in the M3 Message.
GTK is used to protect the Broadcast/MultiCas t Traffic.
IGTK is used to protect Broadcast/multicast Management Frames.
GTK/IGTK will be generated by the AP and it is randomly generated. GTK/IGTK generation function will get the GMK as a seeding material to generate the GTK/IGTK. GMK is also a random value generated at the AP. This GTK/IGTK will be wrapped by the KEK that is generated as a part of PTK and sent in the M3 Message.
In the future there will be a new key that gets wrapped in the M3 Message that is BIGTK, this key will be used to protect the beacon frames. We are not going to discuss about this key in this post.
GTK = PRF-X(GMK, “Group key expansion”, AA || GNonce)
The above function is the GTK/IGTK Generation Function defined by standard, GMK and Gnonce will be generated randomly, AA is the AP MAC Address.
Few Implementations will add few other randomly generated input to get more entropy for GMK.
GTK/IGTK Unwrap
M3 Message in 4-way Hand Shake

KEK (Key Encryption Key) is used to wrap the GTK/IGTK to send client. We will get this KEK from PTK, PTK gets generated at M2.
GTK/IGTK will be wrapped using AES Key Wrap algorithm. Key wrapping is the process of encrypting one key using another key, in order to securely store it or transmit.
Verification of the GTK/IGTK with wireshark
Wireshark has the support to decrypt the WPA2 handshake. It doesn’t have support to decrypt the WPA2-PMF and WPA3 handshake. So, in this example we will take the example M3 message of WPA2 and we will verify only the GTK in this example.
Decryption procedure of M3 message in WPA2-PMF and WPA3 is exactly the same as WPA2. I am using WPA2 here in the example because we can easily verify this with wireshark.
We will take the example of M3 Message in the wireshark and then we will verify this GTK in wireshark. Below figure shows the M3 Message captured in wireshark.

We need a KEK to decrypt the Key data of M3, we need the below input to the AES Key Wrap algorithm. Doing it with a c program will take so much efforts to decrypt the data.
Input to the AES-Key-Wrap.
- WPA Encrypted Key Data.
- KEK (That got Generated from PTK)
Now we will decrypt the M3 message and we will compare the results with wireshark.
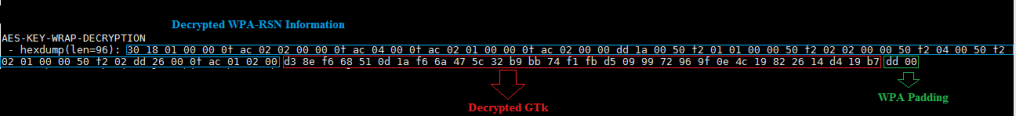
Now lets compare the decrypted results we have got with wireshark, it matches.

Note that Decrypting IGTK is also the same way. But as of now wireshark does not have the support to decrypt WPA2-PMF and WPA3. So, we can’t see the decrypted 4-way handshake in the wireshark. This is all about M3 Message in the 4-way Handshake.